Wipe disks before you recycle them.
Single-file Windows utility. No installer, no nag screens, no upsell. Built because I didn't want to pay for a bloated commercial wiper to do something Windows can already do, just with a worse UI.
Live progress, throughput graphs, and a verification pass.
Per-block speed, stall detection, and tamper-evident certificates. If something's wrong with a wipe, you'll see it while it's happening, not find out later when the cert doesn't match.
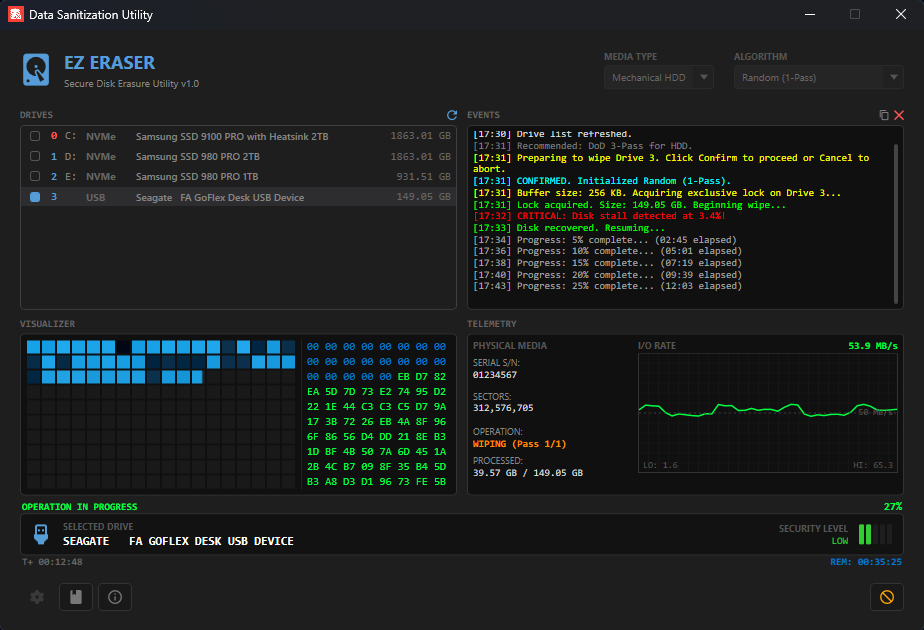
Resume capability
Wipes survive power loss, app crashes, and USB disconnects. State is saved every five seconds, so you can pick up where you left off, even days later. Resume tracking matches drives by serial, model, and capacity, so swapping drives between sessions can't apply state to the wrong target.
{
"DriveModel": "Samsung 980 PRO 1TB",
"Algorithm": "DoD 5220.22-M",
"CompletedPasses": 2,
"CurrentPassOffset": 87432130560,
"LastSavedAt": "2026-05-03T22:11Z"
}
Hardware Secure Erase
For NVMe and SATA drives that support it, EZ Eraser issues firmware-level erase commands instead of software overwrites. NVMe Format with Crypto Erase is near-instant on self-encrypting drives. ATA SECURITY ERASE UNIT clears over-provisioned cells that overwrites can't reach.
opcode = 0x80
SES = 2 // crypto erase preferred
fallback = 1 // user data erase
// drive performs erase internally
// no software overwrites needed
Per-algorithm verification
The verification pass knows what your wipe was supposed to write. Zero Fill verifies all-zeros. VSITR verifies the 0xAA terminator. Random and DoD verify high entropy. Catches drive cache failures, silently skipped bad sectors, and write-pretending USB enclosures.
ZeroWipe → AllZeros
VSITR → AllAA
NIST 800-88 → HighEntropy
DoD 5220.22-M → HighEntropy
Gutmann → HighEntropy
Secure Erase → None
Tamper-evident certificates
Each completed wipe generates an HTML certificate of destruction with a SHA-256 hash computed over drive metadata, algorithm, timestamps, and result. Modify any field on the visible cert and the hash won't match on recomputation, exposing the tampering.
hash = SHA256(
model + "|" +
serial + "|" +
capacity + "|" +
algorithm + "|" +
startTime + "|" +
endTime + "|" +
result
)
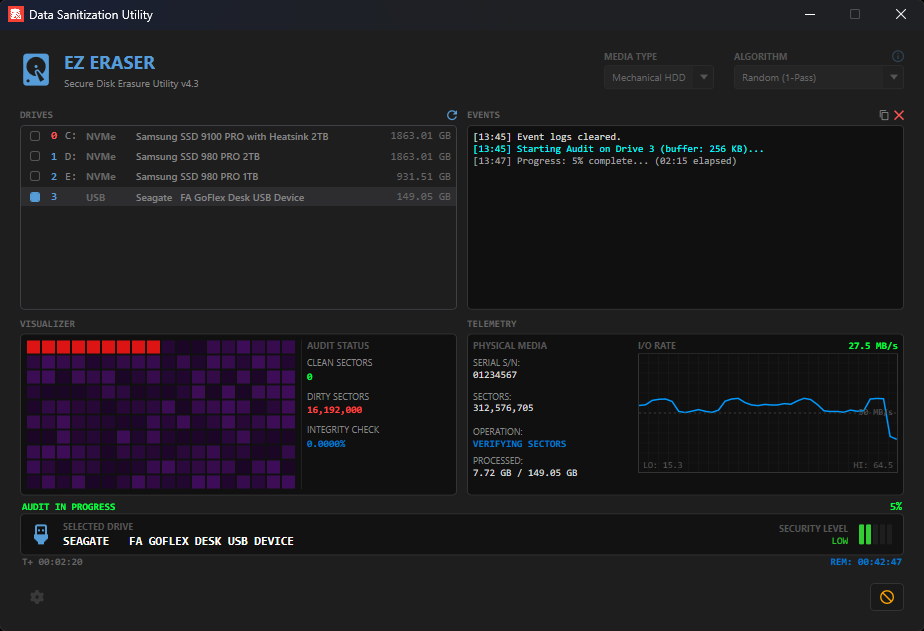
Check a drive without writing to it.
Bought a used drive and want to know if it's actually clean? Audit mode reads every sector and reports clean vs dirty without modifying a single byte.
Ten algorithms.
Most modern drives need a single pass. The multi-pass methods are here for compliance frameworks that pre-date current hardware, not because they're more secure.
Single file. No install.
22FE4D1112B32831866136426ADECA9465CE80D0C720AC8A7E874E52B227C263
Get-FileHash -Algorithm SHA256 .\EzEraser.exe
Found a bug? Got an idea?
This is a hobby project, but I read every issue and email. Bug reports, feature requests, and weird-edge-case drives are all welcome.